cipher
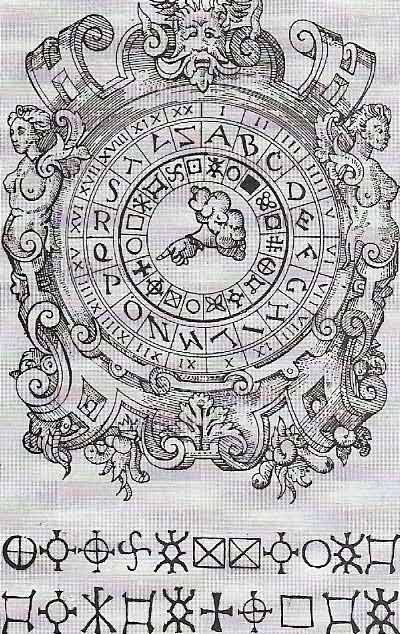
Figure 1. Giovanni Battista Porta (1535–1615), an Italian physicist-inventor, produced one of the earliest substitution ciphers. He used symbols to replace letters and figures. The symbols were chosen by turning the pointer in the center to the necessary letter or number in the two outer rings, then reading off the corresponding symbol in the inner ring. The cipher could be changed at any time by rotating the disks themselves relative to each other, according to a prearranged schedule. The lines of symbols below the disk spell out the inventor's name. A somewhat simpler version was invented Leon Battista Alberti (1404–1472) regarded as the father of cryptography.

Figure 2. An Enigma machine. A series of such electromechanical cipher devices were developed and used in the early- to mid-20th century to protect commercial, diplomatic, and military communications. Enigma was invented by the German engineer Arthur Scherbius and adopted by military and government services of several countries, most notably Nazi Germany, before and during World War II.

Fig 3. The frequency with which letters turn up on average in a English text of 1,000 characters.
In cryptography, a cipher is a cryptographic system in which units of plaintext of regular length, usually letters, are arbitrarily substituted or transposed according to a predetermined code, or a message written or transmitted in such a system.
Substitution cipher
A substitution cipher is a cipher that replaces each plaintext symbol for another, ciphertext symbol (Figure 1). The receiver decodes using the inverse substitution. The Caesar cipher is the simplest and oldest known type of substitution cipher, attributed to Julius Caesar who used it to send government messages. In it, each letter in the alphabet is replaced by another letter using a predefined rule which shifts the alphabet a uniform amount to the right or left. For example, a shift of three units to the right, would turn the "This is secret" into "Wklv lv vhfuhw."
There are some well-known examples of substitution ciphers in fiction being solved based on the fact that the letters of the alphabet are not all used to the same extent. In The Adventure of the Dancing Men by Arthur Conan Doyle, Sherlock Holmes explains how he discovered that the signs of the five dancing men represented the word NEVER. Another famous detective story in which it is shown how to solve a simple code is Edgar Allen Poe's The Gold Bug.
Very few words contain x, z, j, or q. On the other hand, very many contain e, t, i, a, o, n, and s. The table in Figure 3 shows roughly how many times each letter is likely to occur in a message containing 1,000 letters. Of course, you can't expect the letters to turn up always exactly in this proportion. Although e is nearly always the most frequent letter, there are exceptions to this rule. There is, for instance, the well-known verse from the Rubaiyat of Omar Khayyam:
The moving finger writes and having write
Moves on, nor all thy piety nor wit
Shall lure it back to cancel half a line
Nor all they tears wash out a word of it.
In this verse a and t occur 12 times, i, l, n, and o 10 times each, and e only nine times. Another example is Humbert Wolfe's verse:
Thank God! you cannot bribe or twist
The honest British journalist
But seeing what the man will do
Unbribed, there's no occasion to.
This contains t 13 times, o 11 times, n 10 times, and e nine times. In poetry, one is more likely to find unusual results for the number of letters, as a poet may use one particular sound again and again to produce some special effect.
The shorter the message is, the more likely is it that the letters will occur out of their usual frequencies. It is much easier to decode a long message than a short one.
Transposition cipher
A transposition cipher is a cipher that encodes a message by reordering the plaintext. The receiver decodes the message using the inverse transposition. A simple kind of transposition cipher writes the message into a rectangle by rows, for example:
Asimplekin
doftranspo
sitionciph
erwritesth
emessagein
toarectang
lebyrowsan
dreadsitou
tbycolumns
and reads it by columns:
Adsee tldts oirmo erbif tweab eymti rsrya cproi serdo lanta cosle ncegt wiuks iseas tmipp tinao nnohh ngnus.
This type of cipher can be made more difficult to crack by permuting the rows and columns.
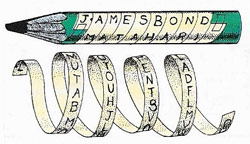 |
| Pencils can be used to make a simple transposition cipher. Write a message on a narrow strip of paper wound in a spiral round one end and send it off. The receiver needs a tube of the same diameter to make sense of it. |
Beale ciphers
The Beale ciphers may be one of the greatest unsolved puzzles in cryptography – or a mere hoax. About a century ago, a fellow by the name of Thomas Beale supposedly buried two wagon-loads of pots filled with silver coin in Bedford County, near Roanoke, Virginia. There are local rumors about the treasure being buried near Bedford Lake. Beale wrote three encoded letters telling what was buried, where it was buried, and to whom it belonged. He entrusted these three letters to a friend, went west, and was never heard from again. Several years later, someone examined the letters and was able to crack the code in the second one, which turned out to be based on the text from the Declaration of Independence. A number in the letter indicated which word in the document was to be used. The first letter of that word replaced the number. For example, if the first three words of the document were "We hold these truths," the number 3 in the letter would represent the letter t. The second letter translated as follows:
I have deposited in the county of Bedford about four miles from Bufords in an excavation or vault six feet below the surface of the ground the following articles belonging jointly to the parties whose names are given in number three herewith. The first deposit consisted of ten hundred and fourteen pounds of gold and thirty eight hundred and twelve pounds of silver deposited Nov eighteen nineteen. The second was made Dec eighteen twenty one and consisted of nineteen hundred and seven pounds of gold and twelve hundred and eighty eight of silver, also jewels obtained in St. Louis in exchange to save transportation and valued at thirteen [t]housand dollars. The above is securely packed i[n] [i]ron pots with iron cov[e]rs. Th[e] vault is roughly lined with stone and the vessels rest on solid stone and are covered [w]ith others. Paper number one describes th[e] exact locality of the va[u]lt so that no difficulty will be had in finding it.
One of the remaining letters supposedly contains directions on how to find the treasure but, to date, no one has solved the code. One theory is that both the remaining letters are encoded using either the same document in a different way, or another very public document. Or, of course, this could all be an elaborate, but entertaining, wheeze. Those interested may wish to contact The Beale Cypher Association, PO Box 975, Beaver Falls, PA 15010.


